Marché irakien de la cybersécurité, par offre (services et solutions/logiciels), application (gestion des identités et des accès, offre de services de sécurité et de confidentialité des données, gouvernance, risque et conformité, offre de services de gestion unifiée des vulnérabilités et autres), type de sécurité (sécurité des infrastructures, sécurité du réseau , sécurité des applications, sécurité du cloud, sécurité des terminaux et autres), modèle de déploiement (cloud et sur site), taille de l'entreprise (grandes entreprises et petites et moyennes entreprises), utilisateur final (industriel, commercial, gouvernemental et résidentiel) - Tendances et prévisions de l'industrie jusqu'en 2029.
Analyse et perspectives du marché de la cybersécurité en Irak
La cybersécurité protège les systèmes connectés à Internet, tels que le matériel, les logiciels et les données, contre les cybermenaces et les violations. L'augmentation des solutions de cybersécurité des services cloud et l'avènement de la culture du travail à distance stimulent le marché. Cependant, l'augmentation des menaces de cybersécurité et des ransomwares dans les solutions de cybersécurité pourrait freiner la croissance.
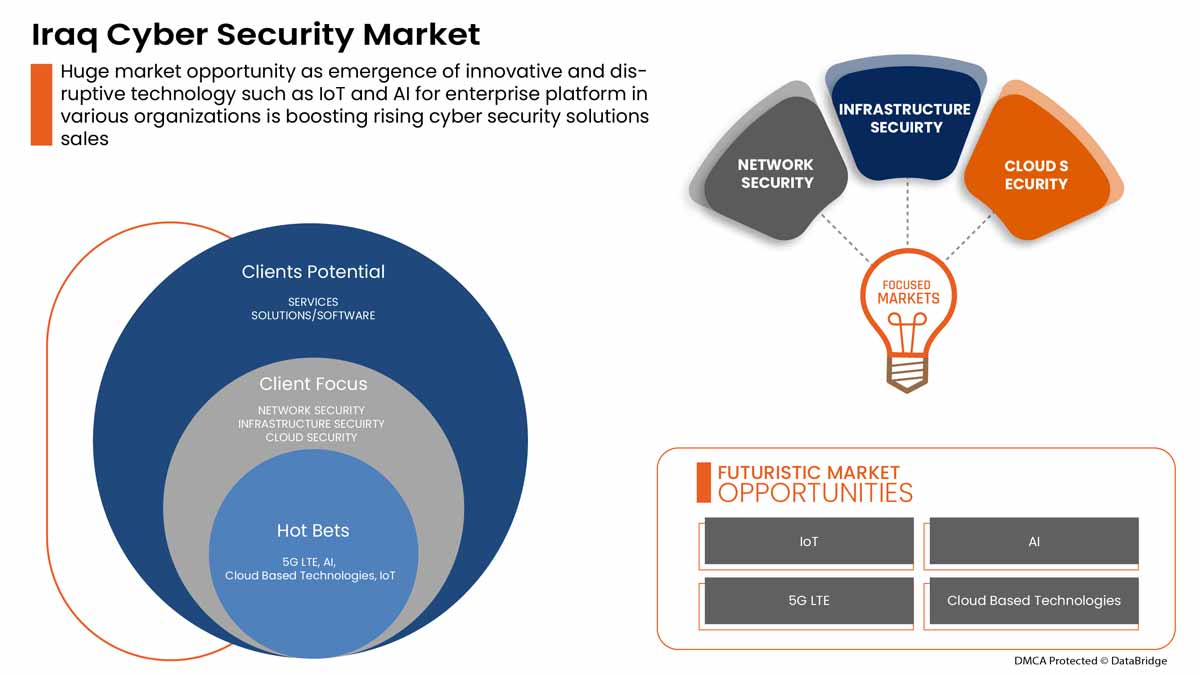
La demande en matière de cybersécurité augmente et continuera de croître à l'avenir. Data Bridge Market Research estime que le marché irakien de la cybersécurité connaîtra un TCAC de 6,3 % entre 2022 et 2029.
|
Rapport métrique |
Détails |
|
Période de prévision |
2022 à 2029 |
|
Année de base |
2021 |
|
Années historiques |
2020 (personnalisable de 2019 à 2014) |
|
Unités quantitatives |
Valeurs en millions |
|
Segments couverts |
Par offre (services et solutions/logiciels), application (gestion des identités et des accès, offre de services de sécurité et de confidentialité des données, gouvernance, risque et conformité, offre de services de gestion unifiée des vulnérabilités et autres), type de sécurité (sécurité de l'infrastructure, sécurité du réseau, sécurité des applications, sécurité du cloud , sécurité des terminaux et autres), modèle de déploiement (cloud et sur site), taille de l'entreprise (grandes entreprises et petites et moyennes entreprises), utilisateur final (industriel, commercial, gouvernemental et résidentiel) |
|
Pays couverts |
Irak |
|
Acteurs du marché couverts |
BAE Systems, Microsoft, McAfee, LLC, Thales, Rapid7, Trend Micro Incorporated, Accenture, Cisco Systems, Inc., IBM Corporation, Oracle, Splunk Inc., Check Point Software Technologies Ltd., Palo Alto Networks, Fortinet, Inc., Juniper Networks, Inc., Micro Focus et Johnson Controls, entre autres |
Définition du marché
La cybersécurité protège les systèmes connectés à Internet, tels que le matériel, les logiciels et les données, contre les cybermenaces et les violations. Les particuliers et les entreprises ont recours à cette pratique pour se protéger contre les accès non autorisés aux centres de données et autres systèmes intelligents. Une approche de cybersécurité réussie comporte plusieurs niveaux de protection répartis sur les ordinateurs, les réseaux, les programmes ou les données que l'on souhaite protéger.
Dynamique du marché de la cybersécurité en Irak
Cette section traite de la compréhension des moteurs, des avantages, des opportunités, des contraintes et des défis du marché. Tout cela est discuté en détail ci-dessous :
Conducteurs
- L'avènement de la culture du travail à distance
Le télétravail est en plein essor en raison de la récente pandémie, qui a contraint les employés à travailler à distance sur leurs sites respectifs. Il y a quelques décennies, la possibilité de travailler en dehors d'un bureau d'entreprise n'était pas considérée comme réalisable, car on pensait que c'était moins efficace. Le travail à distance ne devient courant qu'aujourd'hui en raison des avancées technologiques telles qu'une forte connectivité Internet, qui pourraient servir de base à des solutions et autres.
- Augmentation des solutions de cybersécurité et de sécurité physique des services cloud
La technologie cloud est une technologie en ligne essentielle utilisée dans le monde entier. Elle permet aux utilisateurs d'accéder au stockage, aux fichiers, aux logiciels et aux serveurs à l'aide d'appareils connectés à Internet. Elle signifie également avoir la possibilité de stocker et d'accéder à des données et des programmes via Internet. Contrairement aux méthodes matérielles et logicielles traditionnelles, les technologies cloud peuvent aider les entreprises à rester à la pointe de la technologie sans dépenser beaucoup d'argent en méthodes traditionnelles.

Opportunité
-
Augmentation des partenariats stratégiques et des acquisitions entre organisations pour les systèmes de sécurité physique et cybernétique
La coordination et l'investissement dans les projets sont essentiels pour obtenir des améliorations durables sur le marché de la sécurité physique et cybernétique. Pour cette raison, le gouvernement et d'autres organisations privées s'efforcent, par le biais de partenariats et d'acquisitions, d'accélérer la croissance des industries. Cela contribue à accroître la notoriété et les bénéfices de l'organisation, créant ainsi une marge de manœuvre pour une nouvelle invention dans l'industrie. De plus, grâce aux partenariats, l'entreprise peut investir davantage dans des technologies avancées pour fournir des services et des solutions de sécurité physique et cybernétique plus sûrs et plus fiables.
Retenue/Défi
- Augmentation des menaces de cybersécurité et des ransomwares dans les solutions de sécurité physique et cybernétique
En raison de la COVID-19, la cybercriminalité et les problèmes de cybersécurité ont augmenté de 600 % en 2020. Les failles de sécurité des réseaux sont une faiblesse que les pirates exploitent pour effectuer des actions non autorisées au sein d'un système. Selon Purple Sec LLC, en 2018, les variantes de logiciels malveillants mobiles ont augmenté de 54 %, dont 98 % ciblent les appareils Android. On estime que 25 % des entreprises ont été victimes de crypto-jacking. Diverses entreprises incluent également le secteur de la sécurité.
Impact du Covid-19 sur le marché irakien de la cybersécurité
La COVID-19 a eu un impact positif sur le marché irakien de la cybersécurité. En raison de la COVID-19, la cybercriminalité et les problèmes de cybersécurité ont augmenté de 600 % en 2020. Les failles de sécurité du réseau sont une faiblesse que les pirates exploitent pour effectuer des actions non autorisées au sein d'un système. Selon Purple Sec LLC, en 2018, les variantes de logiciels malveillants mobiles pour mobiles ont augmenté de 54 % en 2018, dont 98 % ciblent les appareils Android. On estime que 25 % des entreprises ont été victimes de crypto-jacking. Diverses entreprises incluent également le secteur de la sécurité.
Développement récent
- En août 2022, Fortinet, Inc. a annoncé un partenariat avec Comcast Business pour fournir aux entreprises un nouvel ensemble de solutions de services d'accès sécurisé (SASE) et de services de sécurité (SSE) pour aider les entreprises à protéger leurs effectifs distribués.
- En mai 2022, Cisco Systems, Inc. a lancé un outil avancé d'évaluation de la cybersécurité. L'objectif principal du lancement de ces solutions était de permettre aux petites et moyennes entreprises (PME) de mieux comprendre leur posture globale en matière de sécurité.
Portée du marché irakien de la cybersécurité
Le marché de la cybersécurité est segmenté en fonction de l'offre, de l'application, du type de sécurité, du modèle de déploiement, de la taille de l'entreprise et de l'utilisateur final. La croissance de ces segments vous aidera à analyser les segments de croissance faibles dans les industries et à fournir aux utilisateurs un aperçu précieux du marché et des informations sur le marché pour les aider à prendre des décisions stratégiques pour identifier les principales applications du marché.
Offre
- Services
- Solutions/logiciels
Sur la base de l’offre, le marché égyptien de la cybersécurité est segmenté en services et solutions/logiciels.
Application
- Gestion des identités et des accès
- Offre de services de sécurité et de confidentialité des données
- Gouvernance, risque et conformité
- Offre de services de gestion unifiée des vulnérabilités
- Autres
Sur la base des applications, le marché égyptien de la cybersécurité est segmenté en gestion des identités et des accès, offre de services de sécurité et de confidentialité des données, gouvernance, risque et conformité, offre de services de gestion unifiée des vulnérabilités et autres.
Type de sécurité
- Sécurité des infrastructures
- Sécurité du réseau
- Sécurité des applications
- Sécurité du cloud
- Sécurité des terminaux
- Autres
Sur la base du type de sécurité, le marché égyptien de la cybersécurité est segmenté en sécurité des infrastructures, sécurité du réseau, sécurité des applications, sécurité du cloud, sécurité des terminaux et autres.
Modèle de déploiement
- Nuage
- Sur site
Sur la base du modèle de déploiement, le marché égyptien de la cybersécurité est segmenté en cloud et sur site.
Taille de l'entreprise
- Grandes entreprises
- Petites et moyennes entreprises
Sur la base de la taille de l'entreprise, le marché égyptien de la cybersécurité est segmenté en grandes entreprises et en petites et moyennes entreprises.
Utilisateur final
- Industriel
- Commercial
- Gouvernement
- Résidentiel
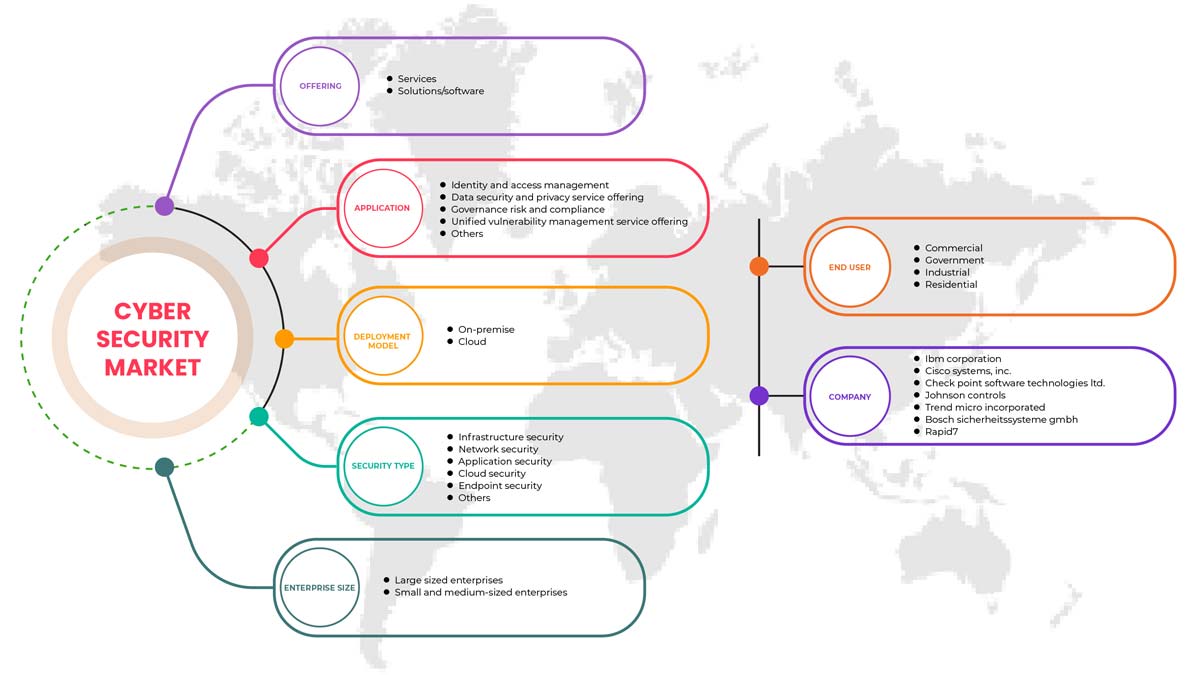
Sur la base du modèle de déploiement, le marché égyptien de la cybersécurité est segmenté en secteurs industriel, commercial, gouvernemental et résidentiel.
Analyse/perspectives régionales du marché de la cybersécurité en Irak
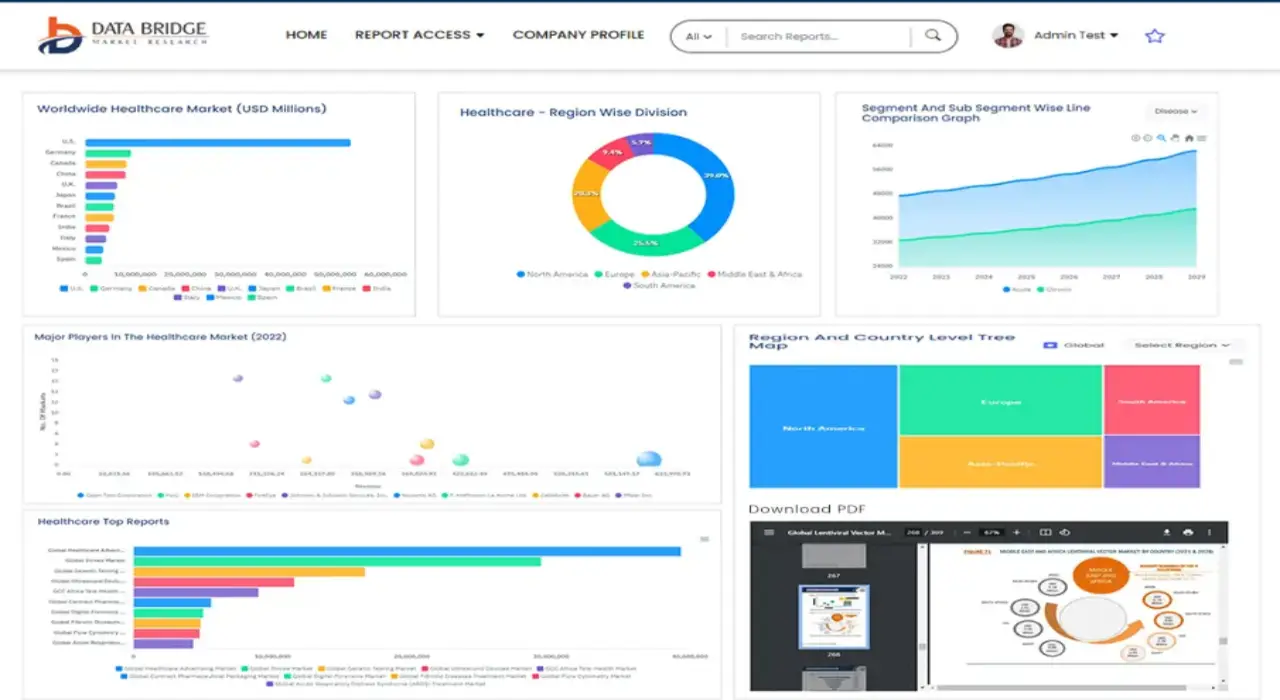
Le marché irakien de la cybersécurité est analysé et des informations sur la taille du marché et les tendances sont fournies par pays, offre, application, type de sécurité, modèle de déploiement, taille de l'entreprise et utilisateur final.
La section par pays du rapport fournit également des facteurs d'impact sur les marchés individuels et des changements de réglementation sur le marché national qui affectent les tendances actuelles et futures du marché. Des points de données tels que les nouvelles ventes, les ventes de remplacement, la démographie des pays, l'épidémiologie des maladies et les tarifs d'importation et d'exportation sont quelques-uns des indicateurs importants utilisés pour prévoir le scénario de marché pour les différents pays. En outre, la présence et la disponibilité des marques mondiales et les défis auxquels elles sont confrontées en raison de la concurrence substantielle ou rare des marques locales et nationales ont un impact sur les canaux de vente tout en fournissant une analyse prévisionnelle des données nationales.
Analyse du paysage concurrentiel et des parts de marché de la cybersécurité en Irak
Le paysage concurrentiel du marché irakien de la cybersécurité fournit des détails sur un concurrent. Les composants inclus sont la présentation de l'entreprise, les finances de l'entreprise, les revenus générés, le potentiel du marché, les investissements dans la recherche et le développement, les nouvelles initiatives du marché, la présence mondiale, les sites et installations de production, les capacités de production, les forces et les faiblesses de l'entreprise, le lancement du produit, la largeur et l'étendue du produit, la domination des applications. Les points de données ci-dessus fournis ne concernent que l'orientation des entreprises sur le marché irakien de la cybersécurité.
Certains des principaux acteurs clés du marché irakien de la cybersécurité sont BAE Systems, Microsoft, McAfee, LLC, Thales, Rapid7, Trend Micro Incorporated, Accenture, Cisco Systems, Inc., IBM Corporation, Oracle, Splunk Inc., Check Point Software Technologies Ltd., Palo Alto Networks, Fortinet, Inc., Juniper Networks, Inc., Micro Focus et Johnson Controls, entre autres.
SKU-
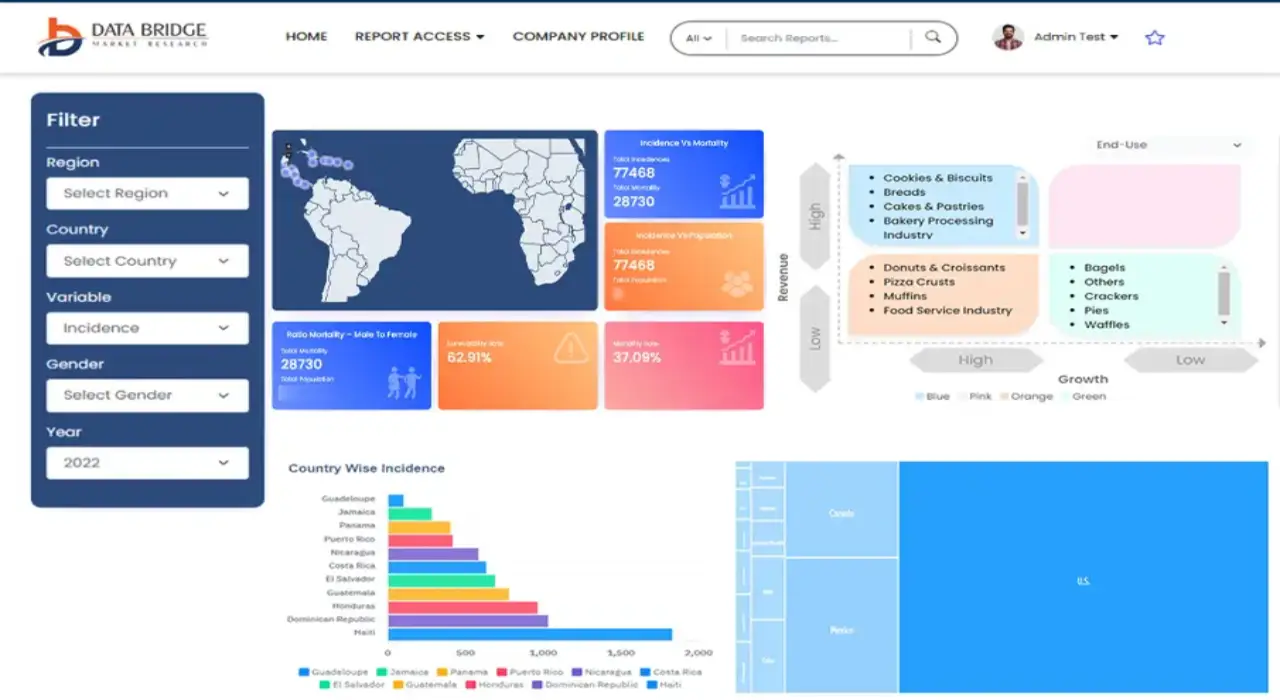
Accédez en ligne au rapport sur le premier cloud mondial de veille économique
- Tableau de bord d'analyse de données interactif
- Tableau de bord d'analyse d'entreprise pour les opportunités à fort potentiel de croissance
- Accès d'analyste de recherche pour la personnalisation et les requêtes
- Analyse de la concurrence avec tableau de bord interactif
- Dernières actualités, mises à jour et analyse des tendances
- Exploitez la puissance de l'analyse comparative pour un suivi complet de la concurrence
Table des matières
1 INTRODUCTION
1.1 OBJECTIVES OF THE STUDY
1.2 MARKET DEFINITION
1.3 OVERVIEW OF IRAQ PHYSICAL AND CYBER SECURITY MARKET
1.4 CURRENCY AND PRICING
1.5 LIMITATIONS
1.6 MARKETS COVERED
2 MARKET SEGMENTATION
2.1 MARKETS COVERED
2.2 GEOGRAPHICAL SCOPE
2.3 YEARS CONSIDERED FOR THE STUDY
2.4 DBMR TRIPOD DATA VALIDATION MODEL
2.5 PRIMARY INTERVIEWS WITH KEY OPINION LEADERS
2.6 DBMR MARKET POSITION GRID
2.7 VENDOR SHARE ANALYSIS
2.8 MARKET END USER COVERAGE GRID
2.9 MULTIVARIATE MODELING
2.1 COMPONENT TIMELINE CURVE
2.11 OFFERING TIMELINE CURVE
2.12 SECONDARY SOURCES
2.13 ASSUMPTIONS
3 EXECUTIVE SUMMARY
4 PREMIUM INSIGHTS
4.1 INVESTMENT POLICY
4.1 CASE STUDY
4.1.1 SECURE SOFTWARE DEVELOPMENT INFRASTRUCTURE
4.1.2 SOC-AS-A-PLATFORM (SOCAAP)
4.1.3 RANSOMWARE & FORENSICS ANALYSIS
4.1.4 WISCONSIN'S DEER DISTRICT SECURITY PLAN
4.1.5 LICENSE PLATE READERS IN SCHOOLS
4.1.6 K-12 SCHOOLS
4.2 VALUE CHAIN ANALYSIS
4.3 PORTERS FIVE FORCES
4.4 PESTLE ANALYSIS
4.5 TECHNOLOGICAL LANDSCAPE
4.5.1 AI AND MACHINE LEARNING
4.5.2 IOT
4.5.3 BLOCKCHAIN
4.6 REGULATORY STANDARDS
4.6.1 CYBER SECURITY
4.6.2 PHYSICAL SECURITY
4.7 LOCAL PLAYERS LIST
5 MARKET OVERVIEW
5.1 DRIVERS
5.1.1 ADVENT OF REMOTE WORKING CULTURE
5.1.2 INCREASE IN CLOUD SERVICES CYBER AND PHYSICAL SECURITY SOLUTIONS
5.1.3 GROWING IMPORTANCE OF PHYSICAL BIOMETRIC SOLUTIONS ACROSS ALL SECTORS
5.1.4 EMERGENCE OF SMART INTERCONNECTED BUILDING/HOME
5.2 RESTRAINTS
5.2.1 RISE IN CYBER SECURITY THREAT AND RANSOMWARE IN PHYSICAL AND CYBER SECURITY SOLUTIONS
5.3 OPPORTUNITIES
5.3.1 RISING STRATEGIC PARTNERSHIP AND ACQUISITION AMONG ORGANIZATIONS FOR PHYSICAL AND CYBER SECURITY SYSTEM
5.3.2 EMERGENCE OF VARIOUS DISRUPTIVE TECHNOLOGY SUCH AS IOT AND AI FOR VARIOUS INDUSTRIES
5.3.3 INCREASE IN CASES OF DATA AND SECURITY BREACHES IN VARIOUS ORGANIZATIONS
5.4 CHALLENGES
5.4.1 LACK OF PROFESSIONAL EXPERTISE FOR CYBER SECURITY SYSTEMS
5.4.2 COMPLEXITY ASSOCIATED WITH THE INTEGRATION OF VARIOUS PHYSICAL SECURITY SYSTEMS
6 IRAQ CYBER SECURITY MARKET, BY OFFERING
6.1 OVERVIEW
6.2 SERVICES
6.3 SOLUTIONS/SOFTWARE
7 IRAQ PHYSICAL SECURITY MARKET, BY COMPONENT
7.1 OVERVIEW
7.2 HARDWARE
7.2.1 VIDEO SURVEILLANCE SYSTEM
7.2.1.1 CAMERAS
7.2.1.2 RECORDERS
7.2.2 PHYSICAL ACCESS CONTROL SYSTEM
7.2.2.1 BIOMETRICS
7.2.2.2 LOCKS
7.2.2.2.1 ELECTRONIC LOCKS
7.3 SERVICES
7.3.1 MANAGED SERVICES
7.3.2 PROFESSIONAL SERVICES
7.4 SOFTWARE
8 IRAQ PHYSICAL SECURITY MARKET, BY AUTHENTICATION
8.1 OVERVIEW
8.2 SINGLE- FACTOR AUTHENTICATION
8.3 TWO- FACTOR AUTHENTICATION
8.4 THREE- FACTOR AUTHENTICATION
9 IRAQ CYBER SECURITY MARKET, BY APPLICATION
9.1 OVERVIEW
9.2 IDENTITY AND ACCESS MANAGEMENT
9.3 DATA SECURITY AND PRIVACY SERVICE OFFERING
9.4 GOVERNANCE RISK AND COMPLIANCE
9.5 UNIFIED VULNERABILITY MANAGEMENT SERVICE OFFERING
9.6 OTHERS
10 IRAQ CYBER SECURITY MARKET, BY SECURITY TYPE
10.1 OVERVIEW
10.2 INFRASTRUCTURE SECURITY
10.3 NETWORK SECURITY
10.4 APPLICATION SECURITY
10.5 CLOUD SECURITY
10.6 ENDPOINT SECURITY
10.7 OTHERS
11 IRAQ PHYSICAL AND CYBER SECURITY MARKET, BY DEPLOYMENT MODEL
11.1 OVERVIEW
11.2 ON-PREMISE
11.3 CLOUD
12 IRAQ PHYSICAL AND CYBER SECURITY MARKET, BY ENTERPRISE SIZE
12.1 OVERVIEW
12.2 LARGE SIZED ENTERPRISES
12.3 SMALL AND MEDIUM-SIZED ENTERPRISES
13 IRAQ PHYSICAL AND CYBER SECURITY MARKET, BY END USER
13.1 OVERVIEW
13.2 COMMERCIAL
13.3 GOVERNMENT
13.4 INDUSTRIAL
13.5 RESIDENTIAL
14 IRAQ CYBER SECURITY MARKET, COMPANY LANDSCAPE
14.1 COMPANY SHARE ANALYSIS: IRAQ
15 IRAQ PHYSICAL SECURITY MARKET, COMPANY LANDSCAPE
15.1 COMPANY SHARE ANALYSIS: IRAQ
16 SWOT ANALYSIS
16.1 DBMR ANALYSIS
16.1.1 STRENGTH
16.1.2 WEAKNESS
16.1.3 THREATS
16.1.4 OPPORTUNITY
17 COMPANY PROFILE
17.1 THALES GROUP
17.1.1 COMPANY SNAPSHOT
17.1.2 REVENUE ANALYSIS
17.1.3 PRODUCTS PORTFOLIO
17.1.4 RECENT DEVELOPMENTS
17.2 HANGZHOU HIKVISION DIGITAL TECHNOLOGY CO., LTD
17.2.1 COMPANY SNAPSHOT
17.2.2 REVENUE ANALYSIS
17.2.3 PRODUCT PORTFOLIO
17.2.4 RECENT DEVELOPMENTS
17.3 ACCENTURE
17.3.1 COMPANY SNAPSHOT
17.3.2 REVENUE ANALYSIS
17.3.3 SERVICE PORTFOLIO
17.3.4 RECENT DEVELOPMENTS
17.4 IDEMIA
17.4.1 COMPANY SNAPSHOT
17.4.2 PRODUCT PORTFOLIO
17.4.3 RECENT DEVELOPMENTS
17.5 BAE SYSTEMS
17.5.1 COMPANY SNAPSHOT
17.5.2 REVENUE ANALYSIS
17.5.3 SERVICE PORTFOLIO
17.5.4 RECENT DEVELOPMENT
17.6 FORTINET, INC.
17.6.1 COMPANY SNAPSHOT
17.6.2 REVENUE ANALYSIS
17.6.3 SERVICE PORTFOLIO
17.6.4 RECENT DEVELOPMENTS
17.7 PALO ALTO NETWORKS
17.7.1 COMPANY SNAPSHOT
17.7.2 REVENUE ANALYSIS
17.7.3 PRODUCT PORTFOLIO
17.7.4 RECENT DEVELOPMENT
17.8 AWARE, INC.
17.8.1 COMPANY SNAPSHOT
17.8.2 REVENUE ANALYSIS
17.8.3 PRODUCT PORTFOLIO
17.8.4 RECENT DEVELOPMENTS
17.9 AXIS COMMUNICATIONS AB
17.9.1 COMPANY SNAPSHOT
17.9.2 REVENUE ANALYSIS
17.9.3 PRODUCT PORTFOLIO
17.9.4 RECENT DEVELOPMENT
17.1 BOSCH SICHERHEITSSYSTEME GMBH
17.10.1 COMPANY SNAPSHOT
17.10.2 REVENUE ANALYSIS
17.10.3 PRODUCTS PORTFOLIO
17.10.4 RECENT DEVELOPMENT
17.11 CHECK POINT SOFTWARE TECHNOLOGIES LTD.
17.11.1 COMPANY SNAPSHOT
17.11.2 REVENUE ANALYSIS
17.11.3 PRODUCTS PORTFOLIO
17.11.4 RECENT DEVELOPMENTS
17.12 CISCO SYSTEMS, INC.
17.12.1 COMPANY SNAPSHOT
17.12.2 REVENUE ANALYSIS
17.12.3 PRODUCTS PORTFOLIO
17.12.4 RECENT DEVELOPMENTS
17.13 HEXAGON AB
17.13.1 COMPANY SNAPSHOT
17.13.2 REVENUE ANALYSIS
17.13.3 OFFERING PORTFOLIO
17.13.4 RECENT DEVELOPMENT
17.14 HID GLOBAL CORPORATION
17.14.1 COMPANY SNAPSHOT
17.14.2 PRODUCT PORTFOLIO
17.14.3 RECENT DEVELOPMENT
17.15 IBM CORPORATION
17.15.1 COMPANY SNAPSHOT
17.15.2 REVENUE ANALYSIS
17.15.3 PRODUCTS PORTFOLIO
17.15.4 RECENT DEVELOPMENTS
17.16 JOHNSON CONTROL
17.16.1 COMPANY SNAPSHOT
17.16.2 REVENUE ANALYSIS
17.16.3 PRODUCTS PORTFOLIO
17.16.4 RECENT DEVELOPMENTS
17.17 JUNIPER NETWORKS, INC.
17.17.1 COMPANY SNAPSHOT
17.17.2 REVENUE ANALYSIS
17.17.3 PRODUCTS PORTFOLIO
17.17.4 RECENT DEVELOPMENTS
17.18 MCAFEE, LLC
17.18.1 COMPANY SNAPSHOT
17.18.2 REVENUE ANALYSIS
17.18.3 PRODUCTS PORTFOLIO
17.18.4 RECENT DEVELOPMENTS
17.19 MICRO FOCUS
17.19.1 COMPANY SNAPSHOT
17.19.2 REVENUE ANALYSIS
17.19.3 PRODUCT PORTFOLIO
17.19.4 RECENT DEVELOPMENT
17.2 MICROSOFT
17.20.1 COMPANY SNAPSHOT
17.20.2 REVENUE ANALYSIS
17.20.3 PRODUCT PORTFOLIO
17.20.4 RECENT DEVELOPMENTS
17.21 ORACLE
17.21.1 COMPANY SNAPSHOT
17.21.2 REVENUE ANALYSIS
17.21.3 SERVICE CATEGORY
17.21.4 RECENT DEVELOPMENT
17.22 PELCO CORPORATIONS
17.22.1 COMPANY SNAPSHOT
17.22.2 REVENUE ANALYSIS
17.22.3 PRODUCTS PORTFOLIO
17.22.4 RECENT DEVELOPMENTS
17.23 RAPID7
17.23.1 COMPANY SNAPSHOT
17.23.2 REVENUE ANALYSIS
17.23.3 PRODUCT PORTFOLIO
17.23.4 RECENT DEVELOPMENTS
17.24 SPLUNK INC.
17.24.1 COMPANY SNAPSHOT
17.24.2 REVENUE ANALYSIS
17.24.3 PRODUCTS PORTFOLIO
17.24.4 RECENT DEVELOPMENT
17.25 TREND MICRO INCORPORATED
17.25.1 COMPANY SNAPSHOT
17.25.2 REVENUE ANALYSIS
17.25.3 PRODUCTS PORTFOLIO
17.25.4 RECENT DEVELOPMENTS
18 QUESTIONNAIRE
19 RELATED REPORTS
Liste des tableaux
TABLE 1 LIST OF LOCAL CYBER SECURITY PLAYERS
TABLE 2 LIST OF LOCAL PHYSICAL SECURITY PLAYERS
TABLE 3 IRAQ CYBER SECURITY MARKET, BY OFFERING, 2020-2029 (USD MILLION)
TABLE 4 IRAQ SERVICES IN CYBER SECURITY MARKET, BY TYPE, 2020-2029 (USD MILLION)
TABLE 5 IRAQ SOLUTIONS/SOFTWARE IN CYBER SECURITY MARKET, BY TYPE, 2020-2029 (USD MILLION)
TABLE 6 IRAQ PHYSICAL SECURITY MARKET, BY COMPONENT, 2020-2029 (USD MILLION)
TABLE 7 IRAQ HARWARE IN PHYSICAL SECURITY MARKET, BY TYPE, 2020-2029 (USD MILLION)
TABLE 8 IRAQ VIDEO SURVEILLANCE SYSTEM IN HARDWRAE PHYSICAL SECURITY MARKET, BY TYPE, 2020-2029 (USD MILLION)
TABLE 9 IRAQ CAMERAS IN VIDEO SURVEILLANCE SYSTEM PHYSICAL SECURITY MARKET, BY TYPE, 2020-2029 (USD MILLION)
TABLE 10 IRAQ RECORDERS IN VIDEO SURVEILLANCE SYSTEM PHYSICAL SECURITY MARKET, BY TYPE, 2020-2029 (USD MILLION)
TABLE 11 IRAQ PHYSICAL ACCESS CONTROL SYSTEM IN PHYSICAL SECURITY MARKET, BY TYPE, 2020-2029 (USD MILLION)
TABLE 12 IRAQ BIOMETRICS IN PHYSICAL ACCESS CONTROL SYSTEM PHYSICAL SECURITY MARKET, BY TYPE, 2020-2029 (USD MILLION)
TABLE 13 IRAQ LOCKS IN PHYSICAL ACCESS CONTROL SYSTEM PHYSICAL SECURITY MARKET, BY TYPE, 2020-2029 (USD MILLION)
TABLE 14 IRAQ ELECTRONIC LOCKS IN LOCKS PHYSICAL SECURITY MARKET, BY TYPE, 2020-2029 (USD MILLION)
TABLE 15 IRAQ SERVICES IN PHYSICAL SECURITY MARKET, BY TYPE, 2020-2029 (USD MILLION)
TABLE 16 IRAQ MANAGED SERVICES IN SERVICES PHYSICAL SECURITY MARKET, BY TYPE, 2020-2029 (USD MILLION)
TABLE 17 IRAQ PROFESSIONAL SERVICES IN SERVICES PHYSICAL SECURITY MARKET, BY TYPE, 2020-2029 (USD MILLION)
TABLE 18 IRAQ SOFTWARE IN PHYSICAL SECURITY MARKET, BY TYPE, 2020-2029 (USD MILLION)
TABLE 19 IRAQ PHYSICAL SECURITY MARKET, BY AUTHENTICATION, 2020-2029 (USD MILLION)
TABLE 20 IRAQ CYBER SECURITY MARKET, BY APPLICATION, 2020-2029 (USD MILLION)
TABLE 21 IRAQ CYBER SECURITY MARKET, BY SECURITY TYPE, 2020-2029 (USD MILLION)
TABLE 22 IRAQ PHYSICAL SECURITY MARKET, BY DEPLOYMENT MODEL, 2020-2029 (USD MILLION)
TABLE 23 IRAQ CYBER SECURITY MARKET, BY DEPLOYMENT MODEL, 2020-2029 (USD MILLION)
TABLE 24 IRAQ PHYSICAL SECURITY MARKET, BY ENTERPRISE SIZE, 2020-2029 (USD MILLION)
TABLE 25 IRAQ CYBER SECURITY MARKET, BY ENTERPRISE SIZE, 2020-2029 (USD MILLION)
TABLE 26 IRAQ LARGE SIZED ENTERPRISES IN PHYSICAL SECURITY MARKET, BY DEPLOYMENT MODEL, 2020-2029 (USD MILLION)
TABLE 27 IRAQ LARGE SIZED ENTERPRISES IN CYBER SECURITY MARKET, BY DEPLOYMENT MODEL, 2020-2029 (USD MILLION)
TABLE 28 IRAQ SMALL AND MEDIUM-SIZED ENTERPRISES IN PHYSICAL SECURITY MARKET, BY DEPLOYMENT MODEL, 2020-2029 (USD MILLION)
TABLE 29 IRAQ SMALL AND MEDIUM-SIZED ENTERPRISES IN CYBER SECURITY MARKET, BY DEPLOYMENT MODEL, 2020-2029 (USD MILLION)
TABLE 30 IRAQ PHYSICAL SECURITY MARKET, BY END USER, 2020-2029 (USD MILLION)
TABLE 31 IRAQ CYBER SECURITY MARKET, BY END USER, 2020-2029 (USD MILLION)
TABLE 32 IRAQ COMMERCIAL IN PHYSICAL SECURITY MARKET, BY TYPE, 2020-2029 (USD MILLION)
TABLE 33 IRAQ COMMERCIAL IN CYBER SECURITY MARKET, BY TYPE, 2020-2029 (USD MILLION)
TABLE 34 IRAQ INDUSTRIAL IN PHYSICAL SECURITY MARKET, BY TYPE 2020-2029 (USD MILLION)
TABLE 35 IRAQ INDUSTRIAL IN CYBER SECURITY MARKET, BY TYPE 2020-2029 (USD MILLION)
TABLE 36 IRAQ RESIDENTIAL IN PHYSICAL SECURITY MARKET, BY TYPE 2020-2029 (USD MILLION)
TABLE 37 IRAQ RESIDENTIAL IN CYBER SECURITY MARKET, BY TYPE 2020-2029 (USD MILLION)
Liste des figures
FIGURE 1 IRAQ PHYSICAL AND CYBER SECURITY MARKET: SEGMENTATION
FIGURE 2 IRAQ PHYSICAL AND CYBER SECURITY MARKET: DATA TRIANGULATION
FIGURE 3 IRAQ PHYSICAL AND CYBER SECURITY MARKET: DROC ANALYSIS
FIGURE 4 IRAQ PHYSICAL SECURITY MARKET: REGIONAL VS COUNTRY ANALYSIS
FIGURE 5 IRAQ CYBER SECURITY MARKET: REGIONAL VS COUNTRY ANALYSIS
FIGURE 6 IRAQ PHYSICAL AND CYBER SECURITY MARKET: COMPANY RESEARCH ANALYSIS
FIGURE 7 IRAQ PHYSICAL AND CYBER SECURITY MARKET: INTERVIEW DEMOGRAPHICS
FIGURE 8 IRAQ PHYSICAL SECURITY MARKET: DBMR MARKET POSITION GRID
FIGURE 9 IRAQ CYBER SECURITY MARKET: DBMR MARKET POSITION GRID
FIGURE 10 IRAQ CYBER SECURITY MARKET: VENDOR SHARE ANALYSIS
FIGURE 11 IRAQ PHYSICAL SECURITY MARKET: VENDOR SHARE ANALYSIS
FIGURE 12 IRAQ PHYSICAL SECURITY MARKET: MARKET END USER COVERAGE GRID
FIGURE 13 IRAQ CYBER SECURITY MARKET: MARKET END USER COVERAGE GRID
FIGURE 14 IRAQ CYBER SECURITY MARKET: SEGMENTATION
FIGURE 15 IRAQ PHYSICAL SECURITY MARKET: SEGMENTATION
FIGURE 16 AN INCREASE IN CLOUD SERVICES CYBER AND PHYSICAL SECURITY SOLUTIONS IS EXPECTED TO DRIVE IRAQ PHYSICAL SECURITY MARKET IN THE FORECAST PERIOD OF 2022 TO 2029
FIGURE 17 EMERGENCE OF SMART INTERCONNECTED BUILDING/HOME IS EXPECTED TO DRIVE IRAQ CYBER SECURITY MARKET IN THE FORECAST PERIOD OF 2022 TO 2029
FIGURE 18 SERVICES SEGMENT IS EXPECTED TO ACCOUNT FOR THE LARGEST SHARE OF IRAQ CYBER SECURITY MARKET IN THE FORECASTED PERIOD OF 2022 & 2029
FIGURE 19 HARDWARE SEGMENT IS EXPECTED TO ACCOUNT FOR THE LARGEST SHARE OF IRAQ PHYSICAL SECURITY MARKET IN THE FORECASTED PERIOD OF 2022 & 2029
FIGURE 20 VALUE CHAIN FOR PHYSICAL AND CYBER SECURITY MARKET
FIGURE 21 PORTERS FIVE FORCES ANALYSIS FOR PHYSICAL AND CYBER SECURITY MARKET
FIGURE 22 PESTLE ANALYSIS FOR PHYSICAL AND CYBER SECURITY MARKET
FIGURE 23 DRIVERS, RESTRAINTS, OPPORTUNITIES, AND CHALLENGES OF IRAQ PHYSICAL AND CYBER SECURITY MARKET
FIGURE 24 KEY STATS OF REMOTE WORK
FIGURE 25 GROWING PREVALENCE OF BIOMETRIC SOLUTIONS AMONG CONSUMER
FIGURE 26 TECHNOLOGY AMALGAMATION IN SMART HOME/ BUILDINGS
FIGURE 27 IMPACT OF CYBER SECURITY THREAT
FIGURE 28 PHISHING ATTACKS REPORTED IN RESPECTIVE COUNTRIES IN Q2, 2021
FIGURE 29 IRAQ CYBER SECURITY MARKET, BY OFFERING, 2021
FIGURE 30 IRAQ PHYSICAL SECURITY MARKET, BY COMPONENT, 2021
FIGURE 31 IRAQ PHYSICAL SECURITY MARKET, BY AUTHENTICATION, 2021
FIGURE 32 IRAQ CYBER SECURITY MARKET: BY APPLICATION, 2021
FIGURE 33 IRAQ CYBER SECURITY MARKET: BY SECURITY TYPE, 2021
FIGURE 34 IRAQ PHYSICAL SECURITY MARKET, BY DEPLOYMENT MODEL, 2021
FIGURE 35 IRAQ CYBER SECURITY MARKET, BY DEPLOYMENT MODEL, 2021
FIGURE 36 IRAQ PHYSICAL SECURITY MARKET, BY ENTERPRISE SIZE, 2021
FIGURE 37 IRAQ CYBER SECURITY MARKET, BY ENTERPRISE SIZE, 2021
FIGURE 38 IRAQ PHYSICAL SECURITY MARKET: BY END USER, 2021
FIGURE 39 IRAQ CYBER SECURITY MARKET: BY END USER, 2021
FIGURE 40 IRAQ CYBER SECURITY MARKET: COMPANY SHARE 2021 (%)
FIGURE 41 IRAQ PHYSICAL SECURITY MARKET: COMPANY SHARE 2021 (%)

Méthodologie de recherche
La collecte de données et l'analyse de l'année de base sont effectuées à l'aide de modules de collecte de données avec des échantillons de grande taille. L'étape consiste à obtenir des informations sur le marché ou des données connexes via diverses sources et stratégies. Elle comprend l'examen et la planification à l'avance de toutes les données acquises dans le passé. Elle englobe également l'examen des incohérences d'informations observées dans différentes sources d'informations. Les données de marché sont analysées et estimées à l'aide de modèles statistiques et cohérents de marché. De plus, l'analyse des parts de marché et l'analyse des tendances clés sont les principaux facteurs de succès du rapport de marché. Pour en savoir plus, veuillez demander un appel d'analyste ou déposer votre demande.
La méthodologie de recherche clé utilisée par l'équipe de recherche DBMR est la triangulation des données qui implique l'exploration de données, l'analyse de l'impact des variables de données sur le marché et la validation primaire (expert du secteur). Les modèles de données incluent la grille de positionnement des fournisseurs, l'analyse de la chronologie du marché, l'aperçu et le guide du marché, la grille de positionnement des entreprises, l'analyse des brevets, l'analyse des prix, l'analyse des parts de marché des entreprises, les normes de mesure, l'analyse globale par rapport à l'analyse régionale et des parts des fournisseurs. Pour en savoir plus sur la méthodologie de recherche, envoyez une demande pour parler à nos experts du secteur.
Personnalisation disponible
Data Bridge Market Research est un leader de la recherche formative avancée. Nous sommes fiers de fournir à nos clients existants et nouveaux des données et des analyses qui correspondent à leurs objectifs. Le rapport peut être personnalisé pour inclure une analyse des tendances des prix des marques cibles, une compréhension du marché pour d'autres pays (demandez la liste des pays), des données sur les résultats des essais cliniques, une revue de la littérature, une analyse du marché des produits remis à neuf et de la base de produits. L'analyse du marché des concurrents cibles peut être analysée à partir d'une analyse basée sur la technologie jusqu'à des stratégies de portefeuille de marché. Nous pouvons ajouter autant de concurrents que vous le souhaitez, dans le format et le style de données que vous recherchez. Notre équipe d'analystes peut également vous fournir des données sous forme de fichiers Excel bruts, de tableaux croisés dynamiques (Fact book) ou peut vous aider à créer des présentations à partir des ensembles de données disponibles dans le rapport.