伊拉克网络安全市场,按产品(服务和解决方案/软件)、应用程序(身份和访问管理、数据安全和隐私服务产品、治理风险和合规性、统一漏洞管理服务产品及其他)、安全类型(基础设施安全、网络安全、应用程序安全、云安全、端点安全及其他)、部署模型(云和本地)、企业规模(大型企业和中小型企业)、最终用户(工业、商业、政府和住宅)划分 - 行业趋势和预测到 2029 年。
伊拉克网络安全市场分析与洞察
网络安全可保护与互联网相连的系统(如硬件、软件和数据)免受网络威胁和入侵。云服务网络安全解决方案的增加和远程工作文化的出现正在推动市场的发展。然而,网络安全威胁和网络安全解决方案中勒索软件的增加可能会抑制增长。
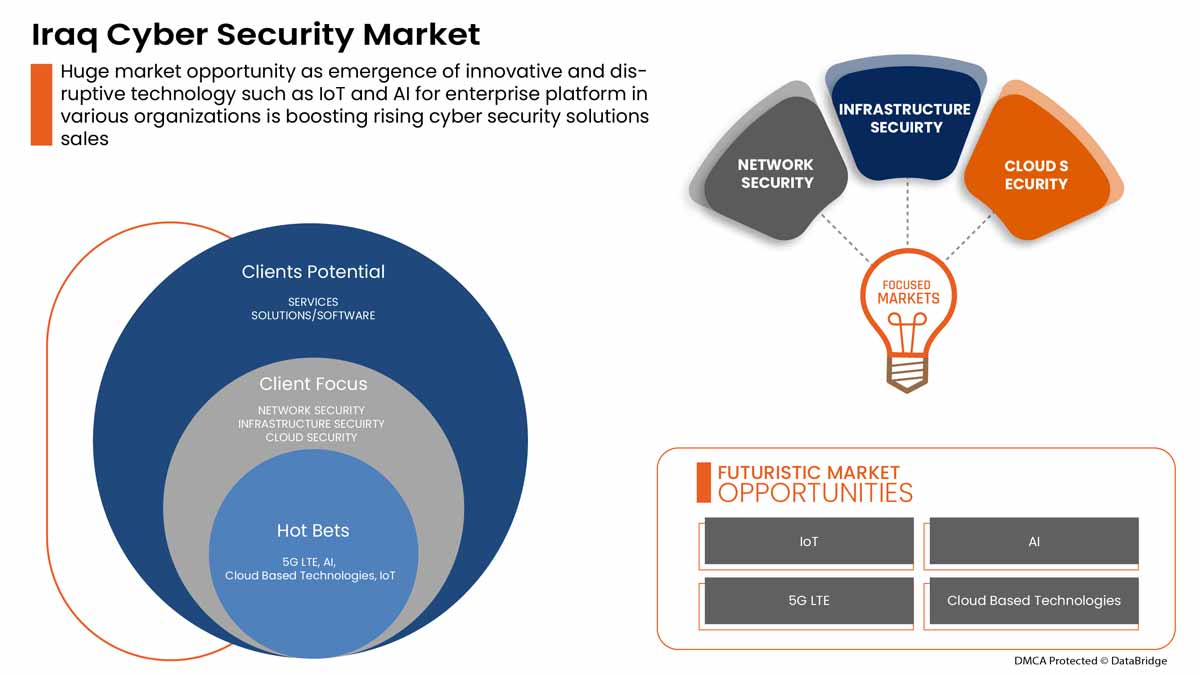
网络安全需求正在增长,未来也将持续增长。Data Bridge Market Research 分析称,2022 年至 2029 年,伊拉克网络安全市场将以 6.3% 的复合年增长率增长。
|
报告指标 |
细节 |
|
预测期 |
2022 至 2029 年 |
|
基准年 |
2021 |
|
历史岁月 |
2020(可定制至 2019 - 2014) |
|
定量单位 |
价值(百万) |
|
涵盖的领域 |
按产品(服务和解决方案/软件)、应用程序(身份和访问管理、数据安全和隐私服务产品、治理风险和合规性、统一漏洞管理服务产品及其他)、安全类型(基础设施安全、网络安全、应用程序安全、云安全、端点安全及其他)、部署模型(云和本地)、企业规模(大型企业和中小型企业)、最终用户(工业、商业、政府和住宅) |
|
覆盖国家 |
伊拉克 |
|
涵盖的市场参与者 |
BAE Systems、Microsoft、McAfee LLC、Thales、Rapid7、Trend Micro Incorporated、埃森哲、思科系统公司、IBM Corporation、甲骨文、Splunk Inc.、Check Point Software Technologies Ltd.、Palo Alto Networks、Fortinet 公司、Juniper Networks 公司、Micro Focus 和 Johnson Controls 等 |
市场定义
网络安全保护与互联网相连的系统(例如硬件、软件和数据)免受网络威胁和入侵。个人和企业使用网络安全措施来防止未经授权访问数据中心和其他智能系统。成功的网络安全方法具有多层保护,涵盖计算机、网络、程序或想要保护的数据。
伊拉克网络安全市场动态
本节旨在了解市场驱动因素、优势、机遇、限制和挑战。下面将详细讨论所有这些内容:
驱动程序
- 远程工作文化的出现
远程工作正在兴起,这是由于最近的疫情,员工被迫在各自的工作地点远程工作。几十年前,在公司办公室外工作被认为是不可行的,因为人们认为这样做效率较低。由于强大的互联网连接等技术进步,远程工作现在才成为主流,这可以为解决方案和其他内容奠定基础。
- 云服务网络和物理安全解决方案的增加
云技术是全球范围内使用的重要在线技术。云技术使用户能够使用互联网连接设备访问存储、文件、软件和服务器。它还意味着或表示能够通过互联网存储和访问数据和程序。与传统的硬件和软件方法不同,云技术可以帮助企业保持技术领先地位,而无需在传统方法上投入大量资金。

机会
-
物理和网络安全系统组织之间的战略伙伴关系和收购增加
协调和投资项目对于实现物理和网络安全市场的持续改善至关重要。因此,政府和其他私人组织正在努力通过合作和收购来加速行业的发展。这有助于为组织建立知名度和利润,从而为行业的新发明创造空间。此外,通过合作伙伴关系,公司可以更多地投资于先进技术,以提供更安全可靠的物理和网络安全市场)服务和解决方案。
克制/挑战
- 物理和网络安全解决方案中网络安全威胁和勒索软件的增加
由于 COVID-19,2020 年网络犯罪和网络安全问题增加了 600%。网络安全漏洞是黑客利用来在系统内执行未经授权的操作的弱点。根据 Purple Sec LLC 的数据,2018 年,针对移动设备的移动恶意软件变种增加了 54%,其中 98% 的移动恶意软件针对 Android 设备。据估计,25% 的企业成为加密劫持的受害者。各种公司还包括安全行业。
Covid-19对伊拉克网络安全市场的影响
COVID-19 对伊拉克网络安全市场产生了积极影响。由于 COVID-19,2020 年网络犯罪和网络安全问题增加了 600%。网络安全漏洞是黑客利用来在系统内执行未经授权的操作的弱点。根据 Purple Sec LLC 的数据,2018 年,移动恶意软件变种增加了 54%,其中 98% 的移动恶意软件针对 Android 设备。据估计,25% 的企业成为加密劫持的受害者。各种公司还包括安全行业。
近期发展
- 2022 年 8 月,Fortinet 公司宣布与 Comcast Business 建立合作伙伴关系,为企业提供一套新的安全访问服务边缘 (SASE) 和安全服务边缘 (SSE) 解决方案,帮助企业保护其分布式员工队伍
- 2022 年 5 月,思科系统公司推出了一款先进的网络安全评估工具。推出该解决方案的主要目的是让中小企业 (SMB) 更好地了解其整体安全状况
伊拉克网络安全市场范围
网络安全市场根据产品、应用、安全类型、部署模式、企业规模和最终用户进行细分。这些细分市场之间的增长情况将帮助您分析行业中增长缓慢的细分市场,并为用户提供有价值的市场概况和市场洞察,帮助他们做出战略决策,确定核心市场应用。
奉献
- 服务
- 解决方案/软件
根据产品供应情况,埃及网络安全市场分为服务和解决方案/软件。
应用
- 身份和访问管理
- 数据安全和隐私服务
- 治理风险与合规
- 统一漏洞管理服务产品
- 其他的
根据应用,埃及网络安全市场细分为身份和访问管理、数据安全和隐私服务产品、治理风险和合规性、统一漏洞管理服务产品等。
安全类型
- 基础设施安全
- 网络安全
- 应用程序安全
- 云安全
- 端点安全
- 其他的
根据安全类型,埃及网络安全市场分为基础设施安全、网络安全、应用程序安全、云安全、端点安全和其他。
部署模型
- 云
- 本地
根据部署模式,埃及网络安全市场分为云端和本地。
企业规模
- 大型企业
- 中小企业
根据企业规模,埃及网络安全市场分为大型企业和中小型企业
最终用户
- 工业的
- 商业的
- 政府
- 住宅
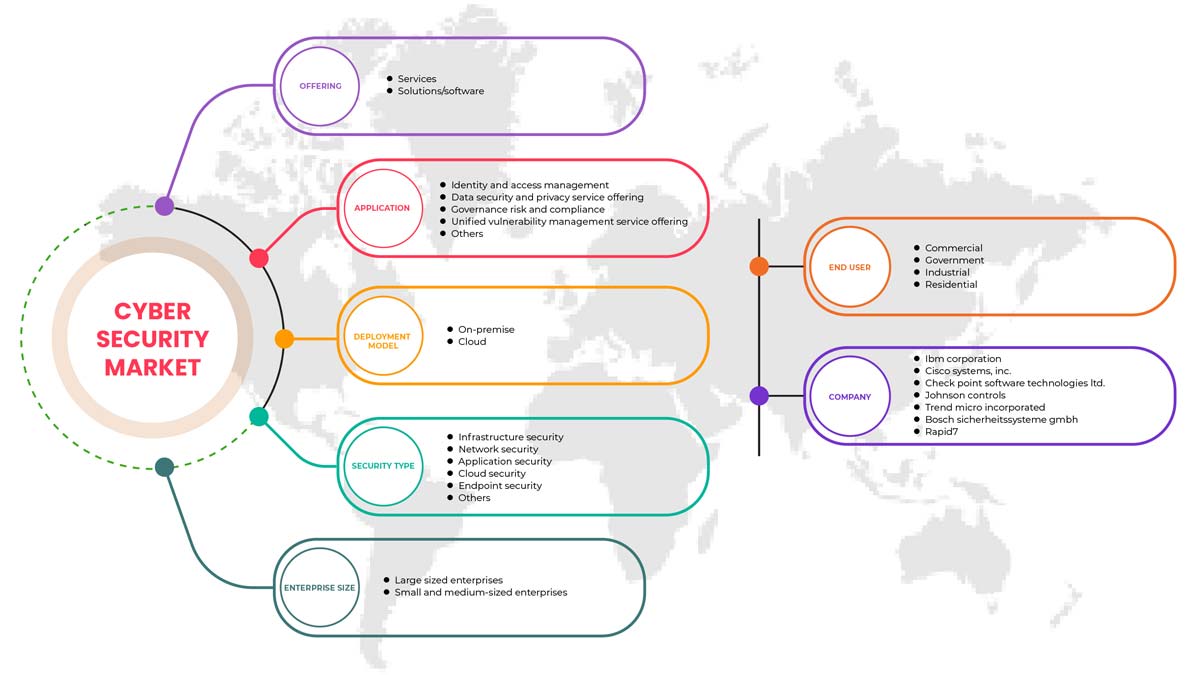
根据部署模式,埃及网络安全市场分为工业、商业、政府和住宅。
伊拉克网络安全市场区域分析/见解
对伊拉克网络安全市场进行了分析,并按国家、产品、应用、安全类型、部署模型、企业规模和最终用户提供了市场规模的见解和趋势。
报告的国家部分还提供了影响单个市场因素和国内市场法规变化,这些变化会影响市场的当前和未来趋势。新销售、替代销售、国家人口统计、疾病流行病学和进出口关税等数据点是用于预测单个国家市场情景的一些重要指标。此外,全球品牌的存在和可用性以及它们因来自本地和国内品牌的大量或稀缺竞争而面临的挑战会影响销售渠道,同时提供国家数据的预测分析。
竞争格局和伊拉克网络安全市场份额分析
伊拉克网络安全市场竞争格局提供了有关竞争对手的详细信息。 其中包括公司概况、公司财务状况、收入、市场潜力、研发投资、新市场计划、全球影响力、生产基地和设施、生产能力、公司优势和劣势、产品发布、产品宽度和广度、应用主导地位。 以上提供的数据点仅与公司对伊拉克网络安全市场的关注有关。
伊拉克网络安全市场的一些主要参与者包括 BAE Systems、Microsoft、McAfee, LLC、Thales、Rapid7、Trend Micro Incorporated、Accenture、Cisco Systems, Inc.、IBM Corporation、Oracle、Splunk Inc.、Check Point Software Technologies Ltd.、Palo Alto Networks、Fortinet, Inc.、Juniper Networks, Inc.、Micro Focus 和 Johnson Controls 等。
SKU-
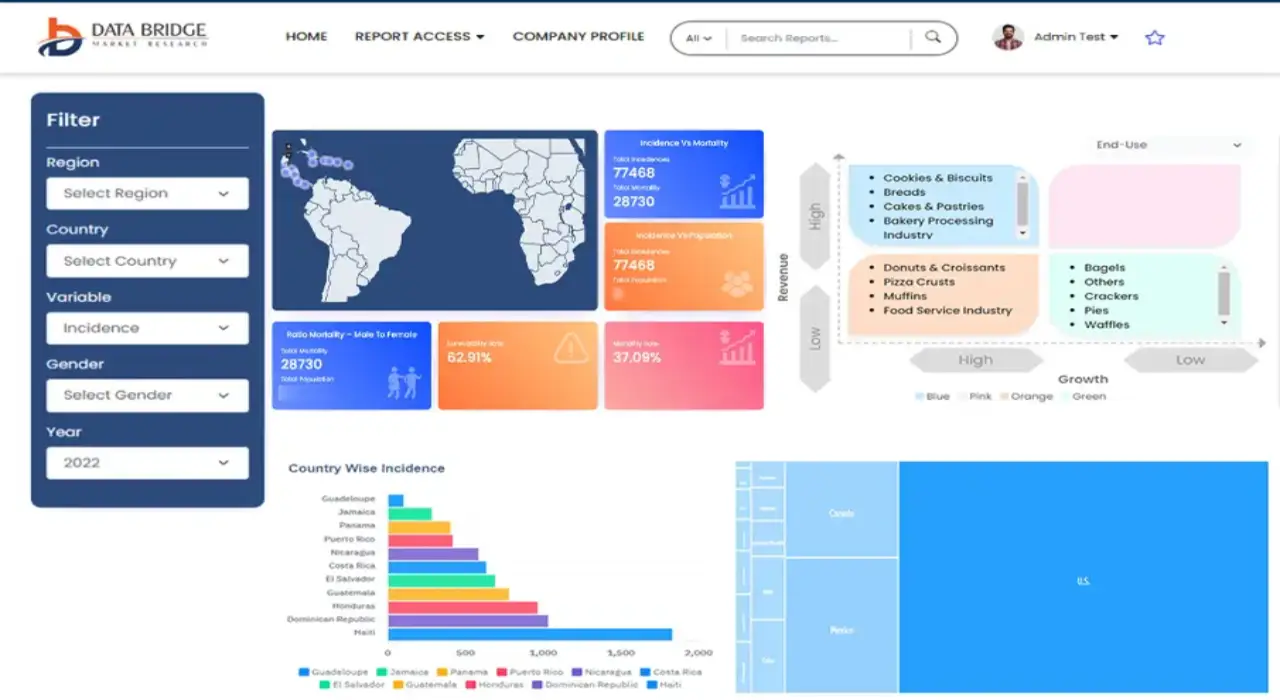
Get online access to the report on the World's First Market Intelligence Cloud
- Interactive Data Analysis Dashboard
- Company Analysis Dashboard for high growth potential opportunities
- Research Analyst Access for customization & queries
- Competitor Analysis with Interactive dashboard
- Latest News, Updates & Trend analysis
- Harness the Power of Benchmark Analysis for Comprehensive Competitor Tracking
目录
1 INTRODUCTION
1.1 OBJECTIVES OF THE STUDY
1.2 MARKET DEFINITION
1.3 OVERVIEW OF IRAQ PHYSICAL AND CYBER SECURITY MARKET
1.4 CURRENCY AND PRICING
1.5 LIMITATIONS
1.6 MARKETS COVERED
2 MARKET SEGMENTATION
2.1 MARKETS COVERED
2.2 GEOGRAPHICAL SCOPE
2.3 YEARS CONSIDERED FOR THE STUDY
2.4 DBMR TRIPOD DATA VALIDATION MODEL
2.5 PRIMARY INTERVIEWS WITH KEY OPINION LEADERS
2.6 DBMR MARKET POSITION GRID
2.7 VENDOR SHARE ANALYSIS
2.8 MARKET END USER COVERAGE GRID
2.9 MULTIVARIATE MODELING
2.1 COMPONENT TIMELINE CURVE
2.11 OFFERING TIMELINE CURVE
2.12 SECONDARY SOURCES
2.13 ASSUMPTIONS
3 EXECUTIVE SUMMARY
4 PREMIUM INSIGHTS
4.1 INVESTMENT POLICY
4.1 CASE STUDY
4.1.1 SECURE SOFTWARE DEVELOPMENT INFRASTRUCTURE
4.1.2 SOC-AS-A-PLATFORM (SOCAAP)
4.1.3 RANSOMWARE & FORENSICS ANALYSIS
4.1.4 WISCONSIN'S DEER DISTRICT SECURITY PLAN
4.1.5 LICENSE PLATE READERS IN SCHOOLS
4.1.6 K-12 SCHOOLS
4.2 VALUE CHAIN ANALYSIS
4.3 PORTERS FIVE FORCES
4.4 PESTLE ANALYSIS
4.5 TECHNOLOGICAL LANDSCAPE
4.5.1 AI AND MACHINE LEARNING
4.5.2 IOT
4.5.3 BLOCKCHAIN
4.6 REGULATORY STANDARDS
4.6.1 CYBER SECURITY
4.6.2 PHYSICAL SECURITY
4.7 LOCAL PLAYERS LIST
5 MARKET OVERVIEW
5.1 DRIVERS
5.1.1 ADVENT OF REMOTE WORKING CULTURE
5.1.2 INCREASE IN CLOUD SERVICES CYBER AND PHYSICAL SECURITY SOLUTIONS
5.1.3 GROWING IMPORTANCE OF PHYSICAL BIOMETRIC SOLUTIONS ACROSS ALL SECTORS
5.1.4 EMERGENCE OF SMART INTERCONNECTED BUILDING/HOME
5.2 RESTRAINTS
5.2.1 RISE IN CYBER SECURITY THREAT AND RANSOMWARE IN PHYSICAL AND CYBER SECURITY SOLUTIONS
5.3 OPPORTUNITIES
5.3.1 RISING STRATEGIC PARTNERSHIP AND ACQUISITION AMONG ORGANIZATIONS FOR PHYSICAL AND CYBER SECURITY SYSTEM
5.3.2 EMERGENCE OF VARIOUS DISRUPTIVE TECHNOLOGY SUCH AS IOT AND AI FOR VARIOUS INDUSTRIES
5.3.3 INCREASE IN CASES OF DATA AND SECURITY BREACHES IN VARIOUS ORGANIZATIONS
5.4 CHALLENGES
5.4.1 LACK OF PROFESSIONAL EXPERTISE FOR CYBER SECURITY SYSTEMS
5.4.2 COMPLEXITY ASSOCIATED WITH THE INTEGRATION OF VARIOUS PHYSICAL SECURITY SYSTEMS
6 IRAQ CYBER SECURITY MARKET, BY OFFERING
6.1 OVERVIEW
6.2 SERVICES
6.3 SOLUTIONS/SOFTWARE
7 IRAQ PHYSICAL SECURITY MARKET, BY COMPONENT
7.1 OVERVIEW
7.2 HARDWARE
7.2.1 VIDEO SURVEILLANCE SYSTEM
7.2.1.1 CAMERAS
7.2.1.2 RECORDERS
7.2.2 PHYSICAL ACCESS CONTROL SYSTEM
7.2.2.1 BIOMETRICS
7.2.2.2 LOCKS
7.2.2.2.1 ELECTRONIC LOCKS
7.3 SERVICES
7.3.1 MANAGED SERVICES
7.3.2 PROFESSIONAL SERVICES
7.4 SOFTWARE
8 IRAQ PHYSICAL SECURITY MARKET, BY AUTHENTICATION
8.1 OVERVIEW
8.2 SINGLE- FACTOR AUTHENTICATION
8.3 TWO- FACTOR AUTHENTICATION
8.4 THREE- FACTOR AUTHENTICATION
9 IRAQ CYBER SECURITY MARKET, BY APPLICATION
9.1 OVERVIEW
9.2 IDENTITY AND ACCESS MANAGEMENT
9.3 DATA SECURITY AND PRIVACY SERVICE OFFERING
9.4 GOVERNANCE RISK AND COMPLIANCE
9.5 UNIFIED VULNERABILITY MANAGEMENT SERVICE OFFERING
9.6 OTHERS
10 IRAQ CYBER SECURITY MARKET, BY SECURITY TYPE
10.1 OVERVIEW
10.2 INFRASTRUCTURE SECURITY
10.3 NETWORK SECURITY
10.4 APPLICATION SECURITY
10.5 CLOUD SECURITY
10.6 ENDPOINT SECURITY
10.7 OTHERS
11 IRAQ PHYSICAL AND CYBER SECURITY MARKET, BY DEPLOYMENT MODEL
11.1 OVERVIEW
11.2 ON-PREMISE
11.3 CLOUD
12 IRAQ PHYSICAL AND CYBER SECURITY MARKET, BY ENTERPRISE SIZE
12.1 OVERVIEW
12.2 LARGE SIZED ENTERPRISES
12.3 SMALL AND MEDIUM-SIZED ENTERPRISES
13 IRAQ PHYSICAL AND CYBER SECURITY MARKET, BY END USER
13.1 OVERVIEW
13.2 COMMERCIAL
13.3 GOVERNMENT
13.4 INDUSTRIAL
13.5 RESIDENTIAL
14 IRAQ CYBER SECURITY MARKET, COMPANY LANDSCAPE
14.1 COMPANY SHARE ANALYSIS: IRAQ
15 IRAQ PHYSICAL SECURITY MARKET, COMPANY LANDSCAPE
15.1 COMPANY SHARE ANALYSIS: IRAQ
16 SWOT ANALYSIS
16.1 DBMR ANALYSIS
16.1.1 STRENGTH
16.1.2 WEAKNESS
16.1.3 THREATS
16.1.4 OPPORTUNITY
17 COMPANY PROFILE
17.1 THALES GROUP
17.1.1 COMPANY SNAPSHOT
17.1.2 REVENUE ANALYSIS
17.1.3 PRODUCTS PORTFOLIO
17.1.4 RECENT DEVELOPMENTS
17.2 HANGZHOU HIKVISION DIGITAL TECHNOLOGY CO., LTD
17.2.1 COMPANY SNAPSHOT
17.2.2 REVENUE ANALYSIS
17.2.3 PRODUCT PORTFOLIO
17.2.4 RECENT DEVELOPMENTS
17.3 ACCENTURE
17.3.1 COMPANY SNAPSHOT
17.3.2 REVENUE ANALYSIS
17.3.3 SERVICE PORTFOLIO
17.3.4 RECENT DEVELOPMENTS
17.4 IDEMIA
17.4.1 COMPANY SNAPSHOT
17.4.2 PRODUCT PORTFOLIO
17.4.3 RECENT DEVELOPMENTS
17.5 BAE SYSTEMS
17.5.1 COMPANY SNAPSHOT
17.5.2 REVENUE ANALYSIS
17.5.3 SERVICE PORTFOLIO
17.5.4 RECENT DEVELOPMENT
17.6 FORTINET, INC.
17.6.1 COMPANY SNAPSHOT
17.6.2 REVENUE ANALYSIS
17.6.3 SERVICE PORTFOLIO
17.6.4 RECENT DEVELOPMENTS
17.7 PALO ALTO NETWORKS
17.7.1 COMPANY SNAPSHOT
17.7.2 REVENUE ANALYSIS
17.7.3 PRODUCT PORTFOLIO
17.7.4 RECENT DEVELOPMENT
17.8 AWARE, INC.
17.8.1 COMPANY SNAPSHOT
17.8.2 REVENUE ANALYSIS
17.8.3 PRODUCT PORTFOLIO
17.8.4 RECENT DEVELOPMENTS
17.9 AXIS COMMUNICATIONS AB
17.9.1 COMPANY SNAPSHOT
17.9.2 REVENUE ANALYSIS
17.9.3 PRODUCT PORTFOLIO
17.9.4 RECENT DEVELOPMENT
17.1 BOSCH SICHERHEITSSYSTEME GMBH
17.10.1 COMPANY SNAPSHOT
17.10.2 REVENUE ANALYSIS
17.10.3 PRODUCTS PORTFOLIO
17.10.4 RECENT DEVELOPMENT
17.11 CHECK POINT SOFTWARE TECHNOLOGIES LTD.
17.11.1 COMPANY SNAPSHOT
17.11.2 REVENUE ANALYSIS
17.11.3 PRODUCTS PORTFOLIO
17.11.4 RECENT DEVELOPMENTS
17.12 CISCO SYSTEMS, INC.
17.12.1 COMPANY SNAPSHOT
17.12.2 REVENUE ANALYSIS
17.12.3 PRODUCTS PORTFOLIO
17.12.4 RECENT DEVELOPMENTS
17.13 HEXAGON AB
17.13.1 COMPANY SNAPSHOT
17.13.2 REVENUE ANALYSIS
17.13.3 OFFERING PORTFOLIO
17.13.4 RECENT DEVELOPMENT
17.14 HID GLOBAL CORPORATION
17.14.1 COMPANY SNAPSHOT
17.14.2 PRODUCT PORTFOLIO
17.14.3 RECENT DEVELOPMENT
17.15 IBM CORPORATION
17.15.1 COMPANY SNAPSHOT
17.15.2 REVENUE ANALYSIS
17.15.3 PRODUCTS PORTFOLIO
17.15.4 RECENT DEVELOPMENTS
17.16 JOHNSON CONTROL
17.16.1 COMPANY SNAPSHOT
17.16.2 REVENUE ANALYSIS
17.16.3 PRODUCTS PORTFOLIO
17.16.4 RECENT DEVELOPMENTS
17.17 JUNIPER NETWORKS, INC.
17.17.1 COMPANY SNAPSHOT
17.17.2 REVENUE ANALYSIS
17.17.3 PRODUCTS PORTFOLIO
17.17.4 RECENT DEVELOPMENTS
17.18 MCAFEE, LLC
17.18.1 COMPANY SNAPSHOT
17.18.2 REVENUE ANALYSIS
17.18.3 PRODUCTS PORTFOLIO
17.18.4 RECENT DEVELOPMENTS
17.19 MICRO FOCUS
17.19.1 COMPANY SNAPSHOT
17.19.2 REVENUE ANALYSIS
17.19.3 PRODUCT PORTFOLIO
17.19.4 RECENT DEVELOPMENT
17.2 MICROSOFT
17.20.1 COMPANY SNAPSHOT
17.20.2 REVENUE ANALYSIS
17.20.3 PRODUCT PORTFOLIO
17.20.4 RECENT DEVELOPMENTS
17.21 ORACLE
17.21.1 COMPANY SNAPSHOT
17.21.2 REVENUE ANALYSIS
17.21.3 SERVICE CATEGORY
17.21.4 RECENT DEVELOPMENT
17.22 PELCO CORPORATIONS
17.22.1 COMPANY SNAPSHOT
17.22.2 REVENUE ANALYSIS
17.22.3 PRODUCTS PORTFOLIO
17.22.4 RECENT DEVELOPMENTS
17.23 RAPID7
17.23.1 COMPANY SNAPSHOT
17.23.2 REVENUE ANALYSIS
17.23.3 PRODUCT PORTFOLIO
17.23.4 RECENT DEVELOPMENTS
17.24 SPLUNK INC.
17.24.1 COMPANY SNAPSHOT
17.24.2 REVENUE ANALYSIS
17.24.3 PRODUCTS PORTFOLIO
17.24.4 RECENT DEVELOPMENT
17.25 TREND MICRO INCORPORATED
17.25.1 COMPANY SNAPSHOT
17.25.2 REVENUE ANALYSIS
17.25.3 PRODUCTS PORTFOLIO
17.25.4 RECENT DEVELOPMENTS
18 QUESTIONNAIRE
19 RELATED REPORTS
表格列表
TABLE 1 LIST OF LOCAL CYBER SECURITY PLAYERS
TABLE 2 LIST OF LOCAL PHYSICAL SECURITY PLAYERS
TABLE 3 IRAQ CYBER SECURITY MARKET, BY OFFERING, 2020-2029 (USD MILLION)
TABLE 4 IRAQ SERVICES IN CYBER SECURITY MARKET, BY TYPE, 2020-2029 (USD MILLION)
TABLE 5 IRAQ SOLUTIONS/SOFTWARE IN CYBER SECURITY MARKET, BY TYPE, 2020-2029 (USD MILLION)
TABLE 6 IRAQ PHYSICAL SECURITY MARKET, BY COMPONENT, 2020-2029 (USD MILLION)
TABLE 7 IRAQ HARWARE IN PHYSICAL SECURITY MARKET, BY TYPE, 2020-2029 (USD MILLION)
TABLE 8 IRAQ VIDEO SURVEILLANCE SYSTEM IN HARDWRAE PHYSICAL SECURITY MARKET, BY TYPE, 2020-2029 (USD MILLION)
TABLE 9 IRAQ CAMERAS IN VIDEO SURVEILLANCE SYSTEM PHYSICAL SECURITY MARKET, BY TYPE, 2020-2029 (USD MILLION)
TABLE 10 IRAQ RECORDERS IN VIDEO SURVEILLANCE SYSTEM PHYSICAL SECURITY MARKET, BY TYPE, 2020-2029 (USD MILLION)
TABLE 11 IRAQ PHYSICAL ACCESS CONTROL SYSTEM IN PHYSICAL SECURITY MARKET, BY TYPE, 2020-2029 (USD MILLION)
TABLE 12 IRAQ BIOMETRICS IN PHYSICAL ACCESS CONTROL SYSTEM PHYSICAL SECURITY MARKET, BY TYPE, 2020-2029 (USD MILLION)
TABLE 13 IRAQ LOCKS IN PHYSICAL ACCESS CONTROL SYSTEM PHYSICAL SECURITY MARKET, BY TYPE, 2020-2029 (USD MILLION)
TABLE 14 IRAQ ELECTRONIC LOCKS IN LOCKS PHYSICAL SECURITY MARKET, BY TYPE, 2020-2029 (USD MILLION)
TABLE 15 IRAQ SERVICES IN PHYSICAL SECURITY MARKET, BY TYPE, 2020-2029 (USD MILLION)
TABLE 16 IRAQ MANAGED SERVICES IN SERVICES PHYSICAL SECURITY MARKET, BY TYPE, 2020-2029 (USD MILLION)
TABLE 17 IRAQ PROFESSIONAL SERVICES IN SERVICES PHYSICAL SECURITY MARKET, BY TYPE, 2020-2029 (USD MILLION)
TABLE 18 IRAQ SOFTWARE IN PHYSICAL SECURITY MARKET, BY TYPE, 2020-2029 (USD MILLION)
TABLE 19 IRAQ PHYSICAL SECURITY MARKET, BY AUTHENTICATION, 2020-2029 (USD MILLION)
TABLE 20 IRAQ CYBER SECURITY MARKET, BY APPLICATION, 2020-2029 (USD MILLION)
TABLE 21 IRAQ CYBER SECURITY MARKET, BY SECURITY TYPE, 2020-2029 (USD MILLION)
TABLE 22 IRAQ PHYSICAL SECURITY MARKET, BY DEPLOYMENT MODEL, 2020-2029 (USD MILLION)
TABLE 23 IRAQ CYBER SECURITY MARKET, BY DEPLOYMENT MODEL, 2020-2029 (USD MILLION)
TABLE 24 IRAQ PHYSICAL SECURITY MARKET, BY ENTERPRISE SIZE, 2020-2029 (USD MILLION)
TABLE 25 IRAQ CYBER SECURITY MARKET, BY ENTERPRISE SIZE, 2020-2029 (USD MILLION)
TABLE 26 IRAQ LARGE SIZED ENTERPRISES IN PHYSICAL SECURITY MARKET, BY DEPLOYMENT MODEL, 2020-2029 (USD MILLION)
TABLE 27 IRAQ LARGE SIZED ENTERPRISES IN CYBER SECURITY MARKET, BY DEPLOYMENT MODEL, 2020-2029 (USD MILLION)
TABLE 28 IRAQ SMALL AND MEDIUM-SIZED ENTERPRISES IN PHYSICAL SECURITY MARKET, BY DEPLOYMENT MODEL, 2020-2029 (USD MILLION)
TABLE 29 IRAQ SMALL AND MEDIUM-SIZED ENTERPRISES IN CYBER SECURITY MARKET, BY DEPLOYMENT MODEL, 2020-2029 (USD MILLION)
TABLE 30 IRAQ PHYSICAL SECURITY MARKET, BY END USER, 2020-2029 (USD MILLION)
TABLE 31 IRAQ CYBER SECURITY MARKET, BY END USER, 2020-2029 (USD MILLION)
TABLE 32 IRAQ COMMERCIAL IN PHYSICAL SECURITY MARKET, BY TYPE, 2020-2029 (USD MILLION)
TABLE 33 IRAQ COMMERCIAL IN CYBER SECURITY MARKET, BY TYPE, 2020-2029 (USD MILLION)
TABLE 34 IRAQ INDUSTRIAL IN PHYSICAL SECURITY MARKET, BY TYPE 2020-2029 (USD MILLION)
TABLE 35 IRAQ INDUSTRIAL IN CYBER SECURITY MARKET, BY TYPE 2020-2029 (USD MILLION)
TABLE 36 IRAQ RESIDENTIAL IN PHYSICAL SECURITY MARKET, BY TYPE 2020-2029 (USD MILLION)
TABLE 37 IRAQ RESIDENTIAL IN CYBER SECURITY MARKET, BY TYPE 2020-2029 (USD MILLION)
图片列表
FIGURE 1 IRAQ PHYSICAL AND CYBER SECURITY MARKET: SEGMENTATION
FIGURE 2 IRAQ PHYSICAL AND CYBER SECURITY MARKET: DATA TRIANGULATION
FIGURE 3 IRAQ PHYSICAL AND CYBER SECURITY MARKET: DROC ANALYSIS
FIGURE 4 IRAQ PHYSICAL SECURITY MARKET: REGIONAL VS COUNTRY ANALYSIS
FIGURE 5 IRAQ CYBER SECURITY MARKET: REGIONAL VS COUNTRY ANALYSIS
FIGURE 6 IRAQ PHYSICAL AND CYBER SECURITY MARKET: COMPANY RESEARCH ANALYSIS
FIGURE 7 IRAQ PHYSICAL AND CYBER SECURITY MARKET: INTERVIEW DEMOGRAPHICS
FIGURE 8 IRAQ PHYSICAL SECURITY MARKET: DBMR MARKET POSITION GRID
FIGURE 9 IRAQ CYBER SECURITY MARKET: DBMR MARKET POSITION GRID
FIGURE 10 IRAQ CYBER SECURITY MARKET: VENDOR SHARE ANALYSIS
FIGURE 11 IRAQ PHYSICAL SECURITY MARKET: VENDOR SHARE ANALYSIS
FIGURE 12 IRAQ PHYSICAL SECURITY MARKET: MARKET END USER COVERAGE GRID
FIGURE 13 IRAQ CYBER SECURITY MARKET: MARKET END USER COVERAGE GRID
FIGURE 14 IRAQ CYBER SECURITY MARKET: SEGMENTATION
FIGURE 15 IRAQ PHYSICAL SECURITY MARKET: SEGMENTATION
FIGURE 16 AN INCREASE IN CLOUD SERVICES CYBER AND PHYSICAL SECURITY SOLUTIONS IS EXPECTED TO DRIVE IRAQ PHYSICAL SECURITY MARKET IN THE FORECAST PERIOD OF 2022 TO 2029
FIGURE 17 EMERGENCE OF SMART INTERCONNECTED BUILDING/HOME IS EXPECTED TO DRIVE IRAQ CYBER SECURITY MARKET IN THE FORECAST PERIOD OF 2022 TO 2029
FIGURE 18 SERVICES SEGMENT IS EXPECTED TO ACCOUNT FOR THE LARGEST SHARE OF IRAQ CYBER SECURITY MARKET IN THE FORECASTED PERIOD OF 2022 & 2029
FIGURE 19 HARDWARE SEGMENT IS EXPECTED TO ACCOUNT FOR THE LARGEST SHARE OF IRAQ PHYSICAL SECURITY MARKET IN THE FORECASTED PERIOD OF 2022 & 2029
FIGURE 20 VALUE CHAIN FOR PHYSICAL AND CYBER SECURITY MARKET
FIGURE 21 PORTERS FIVE FORCES ANALYSIS FOR PHYSICAL AND CYBER SECURITY MARKET
FIGURE 22 PESTLE ANALYSIS FOR PHYSICAL AND CYBER SECURITY MARKET
FIGURE 23 DRIVERS, RESTRAINTS, OPPORTUNITIES, AND CHALLENGES OF IRAQ PHYSICAL AND CYBER SECURITY MARKET
FIGURE 24 KEY STATS OF REMOTE WORK
FIGURE 25 GROWING PREVALENCE OF BIOMETRIC SOLUTIONS AMONG CONSUMER
FIGURE 26 TECHNOLOGY AMALGAMATION IN SMART HOME/ BUILDINGS
FIGURE 27 IMPACT OF CYBER SECURITY THREAT
FIGURE 28 PHISHING ATTACKS REPORTED IN RESPECTIVE COUNTRIES IN Q2, 2021
FIGURE 29 IRAQ CYBER SECURITY MARKET, BY OFFERING, 2021
FIGURE 30 IRAQ PHYSICAL SECURITY MARKET, BY COMPONENT, 2021
FIGURE 31 IRAQ PHYSICAL SECURITY MARKET, BY AUTHENTICATION, 2021
FIGURE 32 IRAQ CYBER SECURITY MARKET: BY APPLICATION, 2021
FIGURE 33 IRAQ CYBER SECURITY MARKET: BY SECURITY TYPE, 2021
FIGURE 34 IRAQ PHYSICAL SECURITY MARKET, BY DEPLOYMENT MODEL, 2021
FIGURE 35 IRAQ CYBER SECURITY MARKET, BY DEPLOYMENT MODEL, 2021
FIGURE 36 IRAQ PHYSICAL SECURITY MARKET, BY ENTERPRISE SIZE, 2021
FIGURE 37 IRAQ CYBER SECURITY MARKET, BY ENTERPRISE SIZE, 2021
FIGURE 38 IRAQ PHYSICAL SECURITY MARKET: BY END USER, 2021
FIGURE 39 IRAQ CYBER SECURITY MARKET: BY END USER, 2021
FIGURE 40 IRAQ CYBER SECURITY MARKET: COMPANY SHARE 2021 (%)
FIGURE 41 IRAQ PHYSICAL SECURITY MARKET: COMPANY SHARE 2021 (%)

研究方法
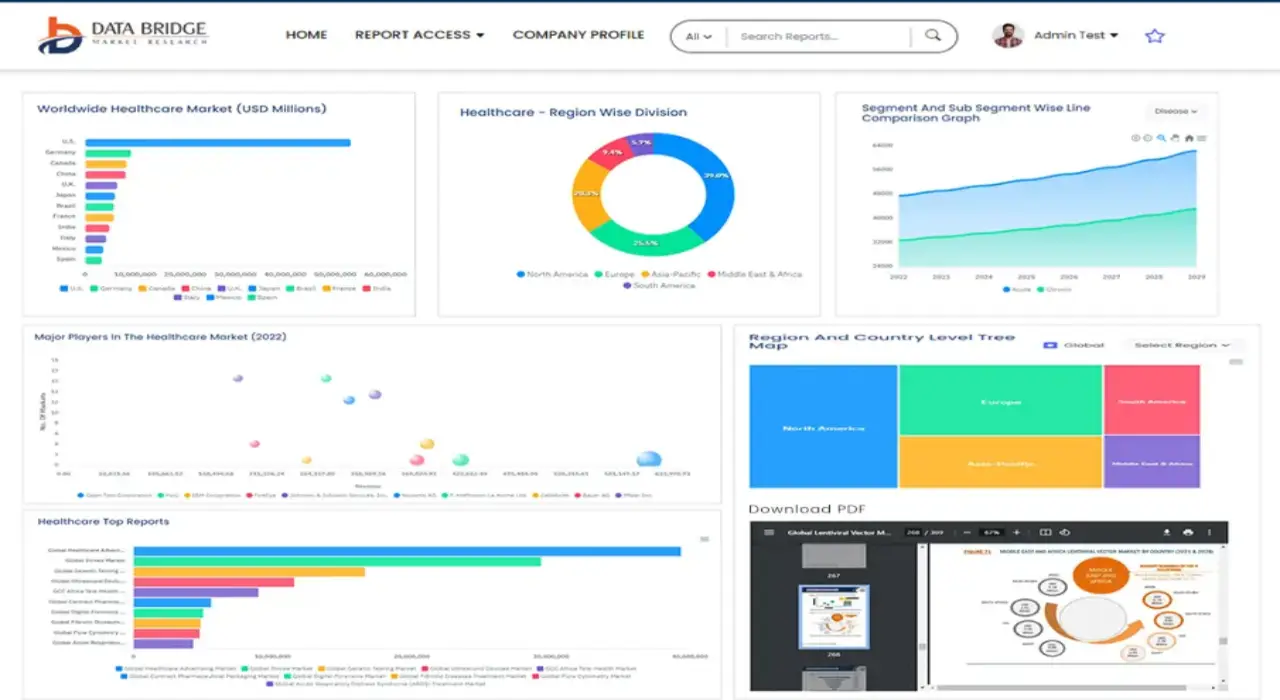
数据收集和基准年分析是使用具有大样本量的数据收集模块完成的。该阶段包括通过各种来源和策略获取市场信息或相关数据。它包括提前检查和规划从过去获得的所有数据。它同样包括检查不同信息源中出现的信息不一致。使用市场统计和连贯模型分析和估计市场数据。此外,市场份额分析和关键趋势分析是市场报告中的主要成功因素。要了解更多信息,请请求分析师致电或下拉您的询问。
DBMR 研究团队使用的关键研究方法是数据三角测量,其中包括数据挖掘、数据变量对市场影响的分析和主要(行业专家)验证。数据模型包括供应商定位网格、市场时间线分析、市场概览和指南、公司定位网格、专利分析、定价分析、公司市场份额分析、测量标准、全球与区域和供应商份额分析。要了解有关研究方法的更多信息,请向我们的行业专家咨询。
可定制
Data Bridge Market Research 是高级形成性研究领域的领导者。我们为向现有和新客户提供符合其目标的数据和分析而感到自豪。报告可定制,包括目标品牌的价格趋势分析、了解其他国家的市场(索取国家列表)、临床试验结果数据、文献综述、翻新市场和产品基础分析。目标竞争对手的市场分析可以从基于技术的分析到市场组合策略进行分析。我们可以按照您所需的格式和数据样式添加您需要的任意数量的竞争对手数据。我们的分析师团队还可以为您提供原始 Excel 文件数据透视表(事实手册)中的数据,或者可以帮助您根据报告中的数据集创建演示文稿。